Blog
Let's better call it "Knowledge-Base".
2021-10-03

What is a Cybersecurity Framework? (ISO 27110)
To address the challenge posed by the constant evolution of cyber threats, business groups, government agencies and other organizations are creating documents and tools called cyber security frameworks.
3 minutes reading time
2021-10-01

What to do With Software From the Last Millennium?
We can migrate or adapt the software and its data. Both ways have advantages and disadvantages. Both are possible with ERP, CRM and other enterprise software.
1 minute reading time
2021-09-27

Are These Dangerous Files?
at.exe ipconfig.exe pathping.exe systeminfo.exe bitsadmin.exe nbtstat.exe ping.exe tasklist.exe certutil.exe net.exe powershell.exe... What are these?
1 minute reading time
2021-09-24

Did Donald Trump win the presidential election because of a cyber attack?
The GU/GRU is an important organ within the Russian military's military intelligence service. In March 2016, it began an operation against the Democratic National Committee (DNC), the governing body of the U.S. Democratic Party. The following text is not about the German federal elections, but how carelessness and fatigue during a cyber attack can have devastating consequences. Perhaps also during an election campaign in Germany?
6 minutes reading time
2021-09-23

Red, Blue, Purple: Are CyberSecurity Teams So Colorful?
Executives often are confused when they want to take care of information security, as they are confronted with unclear terms. Do they need a Purple Team now? Or a security audit? Or a penetration test? First, a tea...
3 minutes reading time
2021-09-21
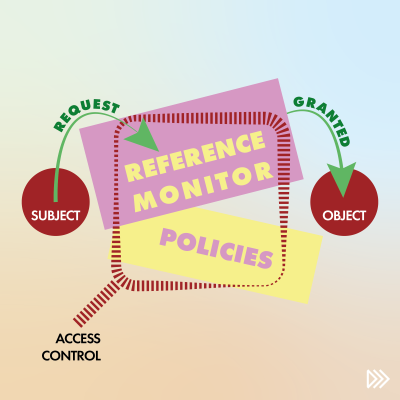
What is a Reference Monitor?
A reference monitor can be an abstract, logical or physical component in a system. As a physical component, think of it like a bouncer in your club: You want to get in? Well, he or she decides. A reference monitor can be implemented anywhere: At the operating system level (e.g., access to files and folders), in your database management system (e.g., an authentication role), in your app, or wherever it's needed. CISSP know this thing.
2 minutes reading time
2021-09-19
Introducing Content Security Policy to Your Website
XSS attacks exploit the browser's trust in the content received from the server. Since the browser trusts the source of the content, malicious scripts are also executed by the user's browser by default. Even if these scripts do not come from where they appear to come from.
3 minutes reading time